A Category-Killing Service at an Unbeatable Price
The Complete Cybersecurity Package, By an SMB for SMBs, at a Reasonable Pricetag
More Tool Integrations Wont Win the War
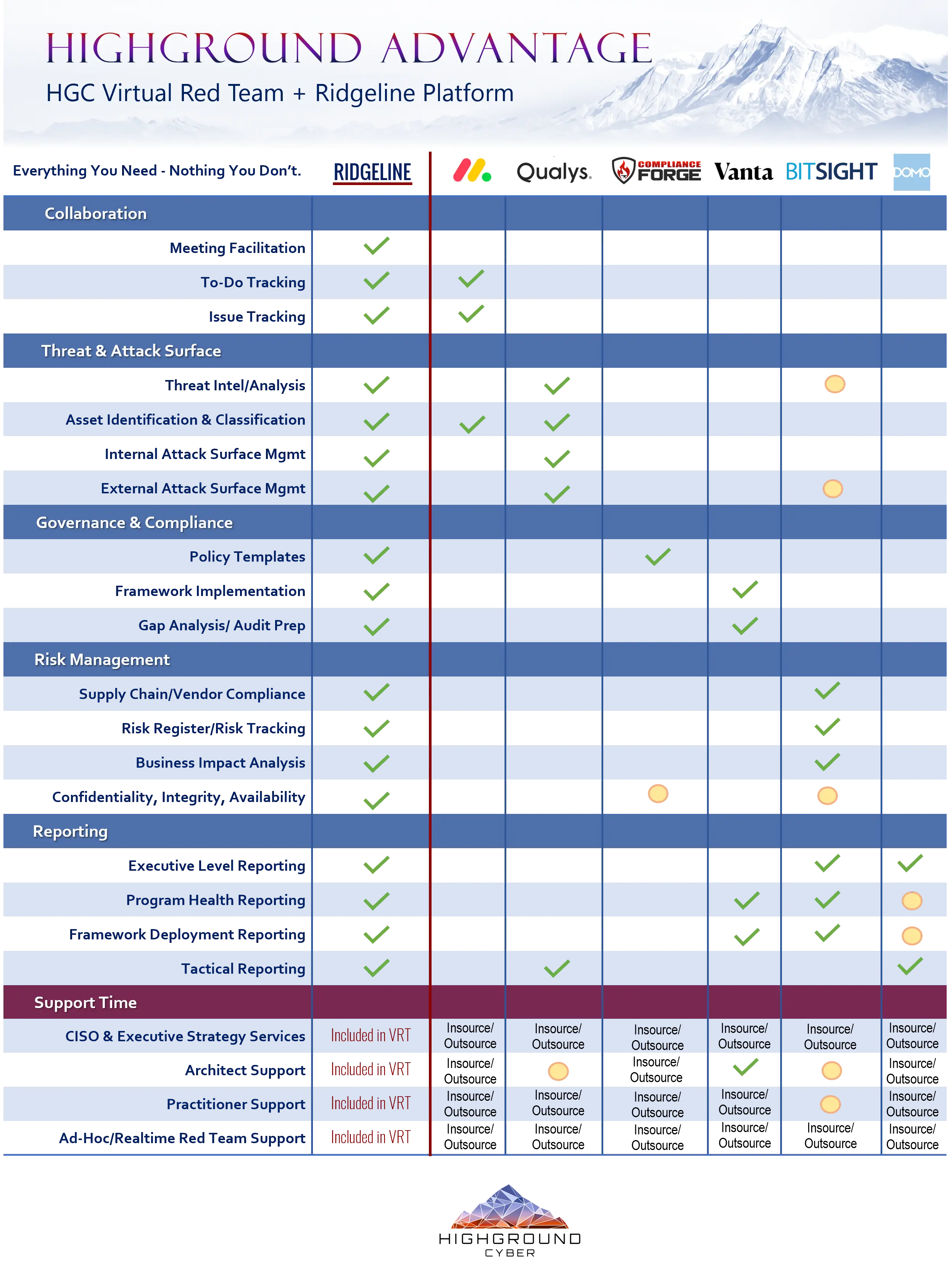
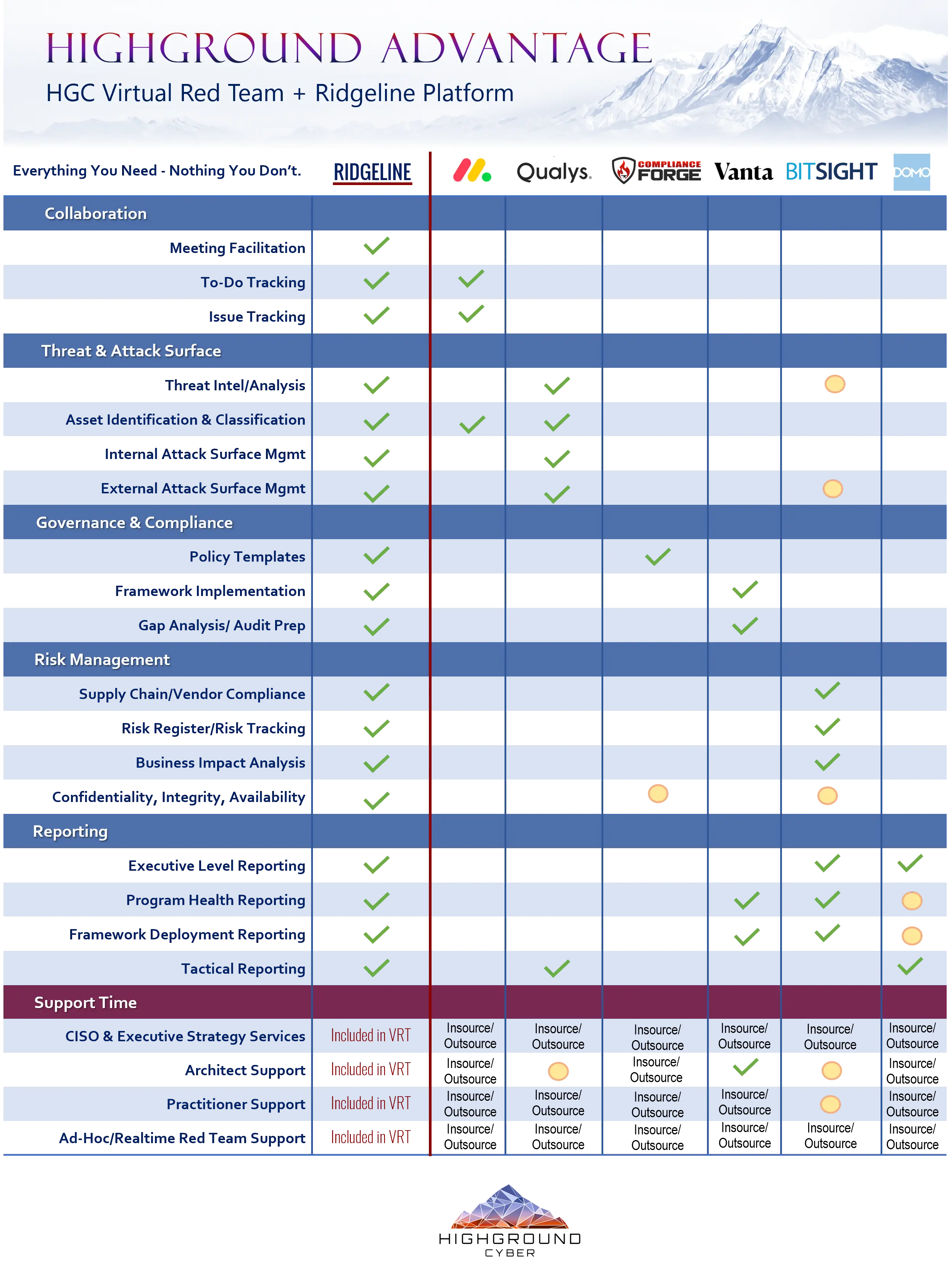
Take a look at what Ridgeline gets you in the graphic below:
The cyber industry is full of several incredibly effective tools and organizations without whom this fight would be utterly hopeless... and it is full of infinitely more
pump-and-dump ventures that are dialing-for-dollars and selling snake oil. Discerning the good from the bad causes so much frustration for non-technical people at the executive
level that it typically ends in them surrendering all of their input as stakeholders and dumping it into the lap of IT. This pattern has been a central point of heartburn that has
done more to damage the credibility and reputation of practitioners in this space than any other single issue at the executive level.
At Highground we believe this buyer's dynamic is dysfunctional, and refuse to participate while many in the space are doubling down on it. The data bears us out on this. When you
see larger percentages of IT budgets being aportioned to cybersecurity year-over-year and then you see sharp increases in the frequency and economic damage of cyber incidents
-instead of decreases- from the companies that are consuming these complex stacks of security tooling: something is fundementally wrong.
In an industry of me-too products all chasing after a handful of pioneer products and industry leaders, the conversation is already going to be slanted toward the only thing they
can control and still compete on: the number of other systems their tool can integrate with, and impressive service metrics on features that may or may not even be relevant to the
problem at hand. They have made this the center of the board in every discussion.
For many of those selling tools, they already know their decisionmaker is going to be technical, and is likely also already responsible for maintaining the infrastructure in
question. They focus on featuresets and integration with other systems and pitch that as the ultimate measure of value, because their target audience is more likely to latch onto
these differances and make their decision at that level of analysis. This issue is not the center of the board, quality metrics on featuresets and integration potential are not good
measures of value if the person selling it to you had no interest in your strategic objectives or interest in the maintainability of your overall architecture. The center of the
board is actually something like "Does this get me closer or further away from my compliance goals? and how would I even be able to tell?" or "does this actually remove operational
liability or change the threat surface of my organization?"
The nature of the current conversation has created a false economy. By becoming an early adopter on that hot new SIEM tool that integrates with everything in a demo environment and
makes use of the most recent security-buzzword technology, you have also perhaps unwittingly swallowed the project time of implementing it into YOUR environment... and the perpetual
resource cost of re-architecting things everytime you touch something in your solution stack that interacts with that SIEM. No one in these conversations is typically willing to ask
the irreverant question of "is this worth the thousands of dollars in resource cost, and the weeks -if not months- long time to value that you aren't quoting me for after I buy this
from you?" or "Who is on the hook to make this work? and how quickly can I expect it to perform as advertised?"
Ridgeline is Ready on Day One
The uncomfortable truth: A fool with a tool is still a fool. A tool will never remove security as a problem. All technology has a hand at the switch somewhere.
The person offering you a demo is rarely the one integrating what they demo, and the capabilities being pitched to you are only as true-to-advirtising as the implementor is capable.
Worse still, they are only as secure as the implementor is knowledgeable of secure configurations.
More often than not, you're buying a pile of raw materials and another professional services bill or internal project to turn those materials into something usable.
Ridgeline is our rebuttal to this failed approach. There will be no integration. There will be no magic solution. There is human work that has to be done, there is a collaboration
space to do it in, there are aids to make the work go faster, and there is reporting on your progress.
You can have it ready-to-go in a single day if needed, you have direct access to the people who develop and maintain it, the more you use it the more powerful it becomes, and it
typically costs less than half the money and none of the time of alternate security solution stacks.
"This is my rifle, there are many like it but this one is mine. Without me my rifle is useless..."
- U.S. Marine Corpse Rifleman's Creed
While Ridgeline confers tremendous leverage to us and our clients when you compare it's capabilities to enable work against other commonly available solution stacks: it is useless
on its own.
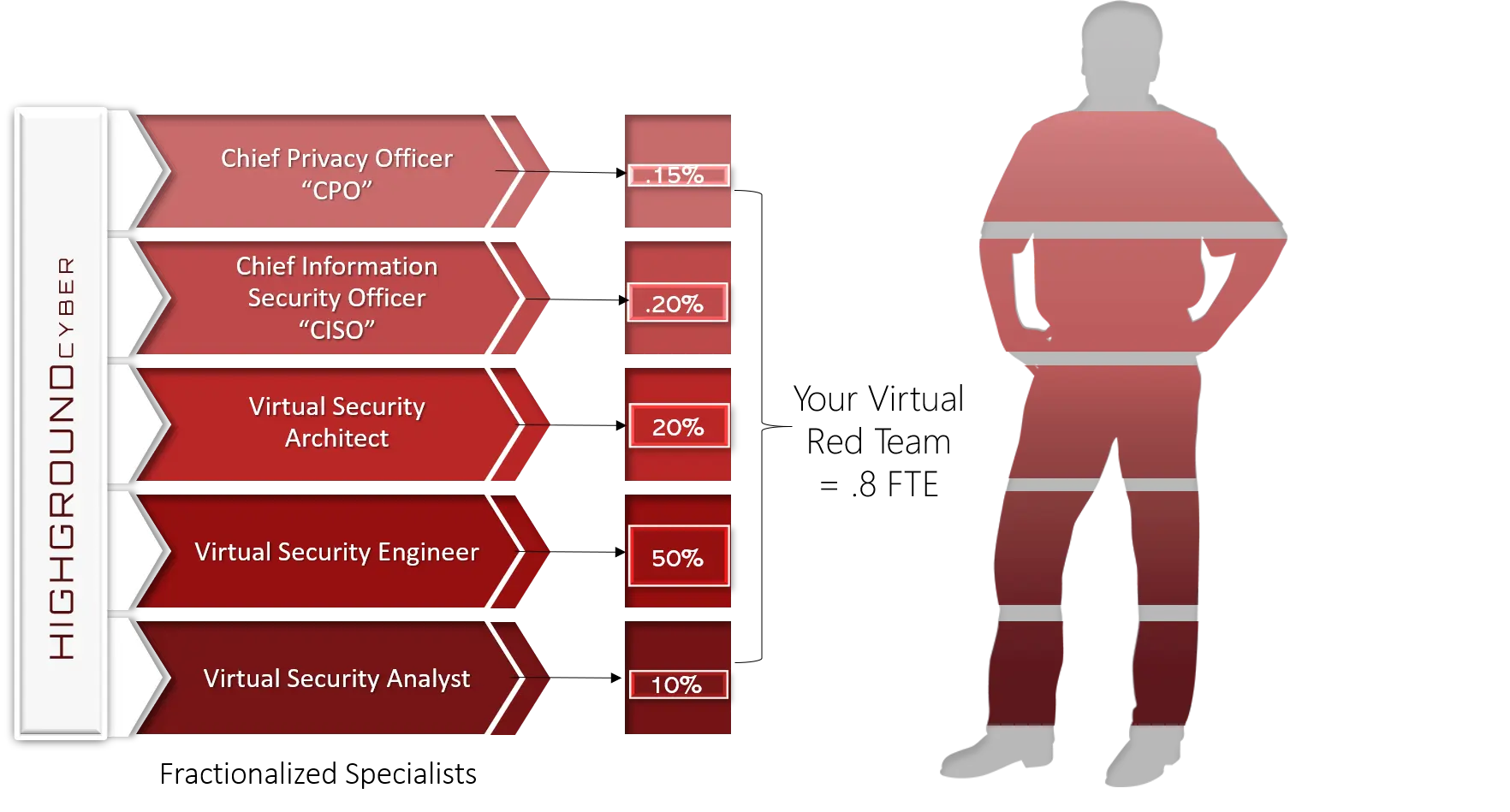
We don't sell Ridgeline, we sell practicioner time.
When you take a second glance at cost comparisons and factor in the hidden resource and time-to-value costs that most people do not anticipate when homebrewing their
cybersecurity/governance programs: paying for a virtual red team with Highground and using Ridgeline is an order of magnitude less burdensome on your organization's cashflow, with
more consistant upfront value delivery and faster results.